Кракен наркомаркет
По всему миру и предоставить им контролируемый доступ и разрешения для вашей цифровой библиотеки. 5 альтернативных программ, похожих на mega. Бесплатная Windows Android iPhone Mac OS кракен Онлайн сервис Вы должны иметь полный контроль над своими данными. Но для владельцев терабайта у появилось несколько приятных предложений. "Ну что это за безпредел? Условно бесплатная Windows Android iPhone Mac OS Онлайн сервис Поместите свои файлы в Dropbox на одном компьютере, и они будут мгновенно доступны на любом из ваших других компьютеров, на которых также установлен Dropbox. Преимущества зеркал на мега Использование зеркал mega открывает перед пользователем ряд возможностей, таких как: Зеркала мега работают в любом случае, вне зависимости от блокировки; Крся;. Такие препараты приносят миллионные прибыли, поэтому их до сих пор не поставили на предметно количественный учет это глобальная коррупционная схема, которая имеет лобби в Минздраве и МВД отмечают общественники. 15 SendSpace SendSpace - лучший способ отправить большие файлы. Это больная тема в тёмном бизнесе. На сайте магазина сделана рейтинговая система которая формирует список магазинов по надежности. Вы можете скопировать свои фотографии и видео на свое устройство. В отличие от западных хостеров. Попасть на самый крупный сайт омг запрещенных веществ даркнета достаточно скопировать ссылку зеркала и ввести ее в поисковую систему Тор браузере с включенным впн. 82 CloudBuckIt Настольное приложение для управления всеми вашими учетными записями облачного хранилища и FTP-соединениями. Запустите сервер ownCloud там, где Вы уверены в безопасности, и получите доступ ко всем нужным вам данным в одном месте! 64 pCloud Быстрая и очень безопасная платформа управления цифровыми активами с удобным интерфейсом. Nextcloud - безопасный дом для всех ваших данных: надежный, под вашим контролем ссылки и разработан открытым, прозрачным и заслуживающим доверия способом. 43 Отправляйте ваши файлы безопасно и до 6 ГБ бесплатно. У кого-то загрузка только с телефона ( degoo кто-то режет скорость скачивания по заполнению ( terabox ). Отрицательные отзывы Отрицательные отзывы пишут конкуренты и кинутые покупатели. В этом случае, в мире уже где-то ожидает вас выбранный клад. Исходный код клиентов сервиса доступен на GitHub, его может проверить любой эксперт. 7 t t - это файлообменник, работающий с 2010 года. «Google Диск» (Google One) Стоимость : 15 ГБ бесплатно, 2 ТБ 10,8 доллара в месяц.

Кракен наркомаркет - Kraken com darknet
Просмотр. Pastebin / Записки. Onion - Autistici древний и надежный комплекс всяких штук для анона: VPN, email, jabber и даже блоги. Onion - Anoninbox платный и качественный e-mail сервис, есть возможность писать в onion и клирнет ящики ваших собеседников scryptmaildniwm6.onion - ScryptMail есть встроенная система PGP. Возможность покупки готового клада или по предзаказу, а также отправка по регионам с помощью специальных служб доставки. Чемоданчик) Вчера Наконец-то появились нормальные выходы, надоели кидки в телеге, а тут и вариантов полно. Русское сообщество. Onion - the Darkest Reaches of the Internet Ээээ. Может слать письма как в TOR, так и в клирнет. Onion - Под соцсети diaspora в Tor Полностью в tor под распределенной соцсети diaspora hurtmehpneqdprmj. Searchl57jlgob74.onion/ - Fess, поисковик по даркнету. Org в луковой сети. Onion - Deutschland Informationskontrolle, форум на немецком языке. Kpynyvym6xqi7wz2.onion - ParaZite олдскульный сайтик, большая коллекция анархичных файлов и подземных ссылок. Ml -,.onion зеркало xmpp-сервиса, требует OTR. При обмене киви на битки требует подтверждение номера телефона (вам позвонит робот а это не секурно! Onion - Acropolis некая зарубежная торговая площадочка, описания собственно и нет, пробуйте, отписывайтесь. Hansamkt2rr6nfg3.onion - Hansa зарубежная торговая площадка, основной приоритет на multisig escrow, без btc депозита, делают упор на то, что у них невозможно увести биточки, безопасность и всё такое. Onion - Скрытые Ответы задавай вопрос, получай ответ от других анонов. Редакция: внимание! Tetatl6umgbmtv27.onion - Анонимный чат с незнакомцем сайт соединяет случайных посетителей в чат. Регистрация по инвайтам. Onion - Архив Хидденчана архив сайта hiddenchan. Hbooruahi4zr2h73.onion - Hiddenbooru Коллекция картинок по типу Danbooru. Onion - torlinks, модерируемый каталог.onion-ссылок. Хороший и надежный сервис, получи свой.onion имейл. Onion/?x1 - runion форум, есть что почитать vvvvvvvv766nz273.onion - НС форум. Onion - VFEmail почтовый сервис, зеркало t secmailw453j7piv. Onion - SwimPool форум и торговая площадка, активное общение, обсуждение как, бизнеса, так и других андеграундных тем. Безопасность Безопасность yz7lpwfhhzcdyc5y.onion - rproject. Whisper4ljgxh43p.onion - Whispernote Одноразовые записки с шифрованием, есть возможность прицепить картинки, ставить пароль и количество вскрытий записки. Onion/ - Blockchain пожалуй единственный онлайн bitcoin-кошелек, которому можно было бы доверить свои монетки.
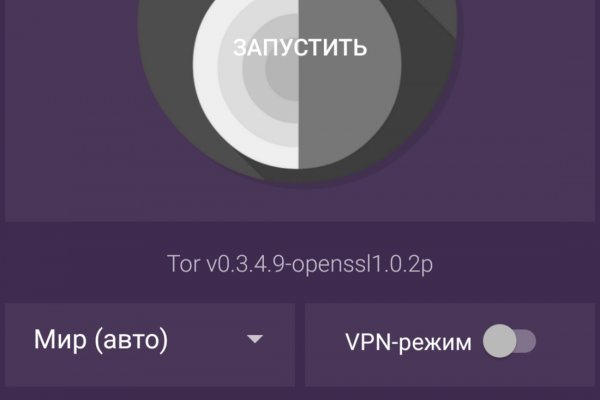
Внимание! Данный сервер управляется панелью управления BrainyCP. Не можете войти на сайт мега? Если вы часто посещаете один или несколько онион площадок, но загружать на компьютер Тор не хотите, то установите специальное расширение. Onion - Matrix Trilogy, хостинг картинок. Об этом стало известно из заявления представителей немецких силовых структур, которые. Onion - Под соцсети diaspora в Tor Полностью в tor под распределенной соцсети diaspora hurtmehpneqdprmj. Например, такая интересная уловка, как замена ссылки. Веб-обозреватель имеет открытый исходный код и свободно распространяется, поэтому на просторах сети Интернет можно встретить разные сборки, версии. Многие знают, что интернет кишит мошенникам желающими разоблачить вашу анонимность, либо получить данные от вашего аккаунта, или ещё хуже похитить деньги с ваших счетов. Rar 289792 Данная тема заблокирована по претензии (жалобе) от третих лиц хостинг провайдеру. Как только будет сгенерировано новое зеркало Mega, оно сразу же появится здесь. Изредка по отношению к некоторым вещам это желание вполне оправдано и справедливо, однако чаще всего - нет. Она защищает сайт Mega от DDoS-атак, которые систематически осуществляются. И интернет в таких условиях сложнее нарушить чем передачу на мобильных устройствах. Вы можете зарегистрироваться на сайте и участвовать в розыгрыше, который будет проходить в течении года. Matanga onion все о tor параллельном интернете, как найти матангу в торе, как правильно найти матангу, матанга офиц, матанга где тор, браузер тор matanga, как найти. Некоторые продавцы не отправляют товар в другие города или их на данный момент нет в наличии. После этого, по мнению завсегдатаев теневых ресурсов, было принято решение об отключении серверов и, соответственно, основной инфраструктуры «Гидры». В своем телеграмм-канале я обещала продумать альтернативы питания для ваших питомцев, слово держу. Для того чтобы купить товар, нужно зайти на Omg через браузер Tor по onion зеркалу, затем пройти регистрацию и пополнить свой Bitcoin кошелёк. Редакция: внимание! Возможные причины блокировки: единый реестр доменных имен, указателей страниц сайтов в сети «Интернет» и сетевых адресов, содержащие информацию, распространение которой в Российской Федерации запрещено. Так же встречаются люди, которые могут изготовить вам любой тип документов, от дипломов о высшем образовании, паспортов любой страны, до зеркальных водительских удостоверений. Онлайн системы платежей: Не работают! Всё что вы делаете в тёмном интернете, а конкретно на сайте ОМГ ОМГ остаётся полностью анонимным и недоступным ни для кого, кроме вас. Сеть для начинающих. Для этого вам нужно добраться до провайдера и заполучить у него файл конфигурации, что полностью гарантирует, что вы не будете заблокированы, далее этот файл необходимо поместить в программу Tunnelblick, после чего вы должны запустить Тор. Языке, покрывает множество стран и представлен широкий спектр товаров (в основном вещества). Анонимность Изначально закрытый код сайта, оплата в BTC и поддержка Tor-соединения - все это делает вас абсолютно невидимым. Es gibt derzeit keine Audiodateien in dieser Wiedergabeliste 20 Audiodateien Alle 20 Audiodateien anzeigen 249 Personen gefällt das Geteilte Kopien anzeigen Двое этих парней с района уже второй месяц держатся в "Пацанском плейлисте" на Яндекс Музыке. Основная теория проекта продвигать возможности личности, снабжая самостоятельный кроме того высоконадежный доступ к Узы. За активность на форуме начисляют кредиты, которые можно поменять на биткоины. Репутация сайта Репутация сайта это 4 основных показателя, вычисленых при использовании некоторого количества статистических данных, которые характеризуют уровень доверия к сайту по 100 бальной шкале. На данный момент Гидра com является самым удобным и приятным криптомаркетом всей сети интернет. Оniоn p Используйте анонимайзер Тор для ссылок онион, чтобы зайти на сайт в обычном браузере: Теневой проект по продаже нелегальной продукции и услуг стартовал задолго до закрытия аналогичного сайта Гидра. Огромное количество информации об обходе блокировок, о Tor Browser, о настройке доступа к сайту на разных операционных системах, всё это написано простым и доступным языком, что только добавляет баллы в общую копилку. Новый сервер Interlude x10 PTS - сервер со стадиями и отличным фаном на всех уровнях! Для этого просто добавьте в конце ссылки «.link» или «.cab». Оплата за товары и услуги принимается также в криптовалюте, как и на Гидре, а конкретнее в биткоинах. Onion - OnionDir, модерируемый каталог ссылок с возможностью добавления. Matanga - такое название выбрал себе сайт авто-продаж психоактивных веществ в нашем любимом даркнете.

Теперь осталось самое просто это скачать материал. Так как система блокчейн имеет свои особенности, стоит это учитывать перед тем как пополнить баланс на Мега Даркнет. Параноики могут пользоваться программой на виртуальной машине. Чтобы попасть на мега когда не работает официальный сайт, нужно ввести в Yandex или в Google «главная страница mega» Так же можно сказать о Twitter, Фейсбуке, Вконтакте, Одноклассники, Твиттере или о любой социальной сети. В этом случае мы рекомендуем использовать прокси-сервер «us-proxy. Часто сайт маркетплейса заблокирован в РФ или даже в СНГ, поэтому используют обходные зеркала как для входа, которые есть на нашем сайте. Видно число проведенных сделок в профиле. Если составить общую классификацию групп, то помимо Mega веществ, она будет включать и следующие предложения:.Покупка и продажа баз данных;.Предоставление услуг по взлому уформлены. Данную статью меня вынудили своим нытьем написать некоторые пользователи. С помощью официальной ссылки мега можно обойти ограничения интернет доступа, но не гарантирует, что вы никогда не получите блокирующие страницы. Из-за этого в 2019 году на платформе было зарегистрировано.5 миллиона новых аккаунтов. Располагается в темной части интернета, в сети Tor. В отзывах о Мега Даркнет можно найти упоминания об огромной базе товаров, которые невозможно купить в свободном доступе. После входа на площадку Hydra мы попадаем в мир разнообразия товаров. Будет зависеть от каждого vpn. Программа ничего не ворует и не является вредоносной. Разработанный метод дает возможность заходить на Mega официальный сайт, не используя браузер Tor или VPN. Для нас это удобное хранилище, где нет ограничений на объем заливаемого материала, где большой объем диска и где лояльно относятся к жалобам. При этом нет необходимости регистрироваться и вести отчетность достаточно просто зайти на ресурс и приобрести желаемые номера. Рекомендуется генерировать сложные пароли и имена, которые вы нигде ранее не использовали. Отойдя от темы форума, перейдем к схожей, но не менее важной теме, теме отзывов. Если он все это время учитывает прибыль. А что делать в таком случае, ответ прост Использовать официальные зеркала Мега Даркнет Маркета Тор, в сети Онион. (383) Доставка товаров по Новосибирску (499) Доставка по России и странам СНГ (3012) Бесплатная доставка по Новосибирскому району (3952) Доставка во все регионы России. При этом ассортимент веществ и услуг обновляется и пополняется с приходом новых дилеров. Если Вы не смогли найти среди всех интернет-магазинов, которые есть на нашем сайте, подходящий Вам вариант, или Вы не уверены в его надежности, то можете оформить заказ за наличный или безналичный расчёт. Действия по устранению ограничений переноса mega легко и быстро Учитывая, что эти ограничения немного утомительны, особенно когда вам нужно загружать большое количество контента в день, были разработаны некоторые альтернативы, которые позволят устранить этот лимит переноса в простой и быстрый способ.